 With Microsoft Dynamics GP, there are only two user accounts which can, by default, create new users or assign access to companies; these the the sa (SQL Server System Administrator) and DYNSA (Dynamics GP System Administrator).
With Microsoft Dynamics GP, there are only two user accounts which can, by default, create new users or assign access to companies; these the the sa (SQL Server System Administrator) and DYNSA (Dynamics GP System Administrator).
The former account should only be used when absolutely necessary (such as when implementing Microsoft Dynamics GP or moving it to a new SQL Server Instance; there are some ISV products which also insist on the sa account when it isn’t strictly necessary from a tecHnical perspective).
The recommended way of maintaining security is to configure a normal user account with the permissions necessary to create and assign users to companies. There are a few steps to go through to assign the relevant security.
Mark Polino did a post a while ago on adding users without using the sa account, but, in this post, Mark assigned the sysadmin role to the user. While this will do the job, and in fewer steps, I prefer to lock down security so users only have the permissions required, which precludes assigning a sysadmin role. The reason for this is both best practice, but also that I have several clients who will not allow the sysadmin role to be assigned to a GP user.
The following steps cover the minimum security required for a user to be able to add new users or assign them access to companies.
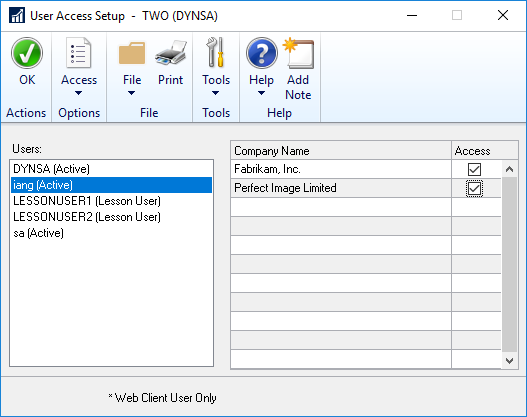
Assign the user to all companies in Microsoft Dynamics GP (this is done in the User Access Setup window ():
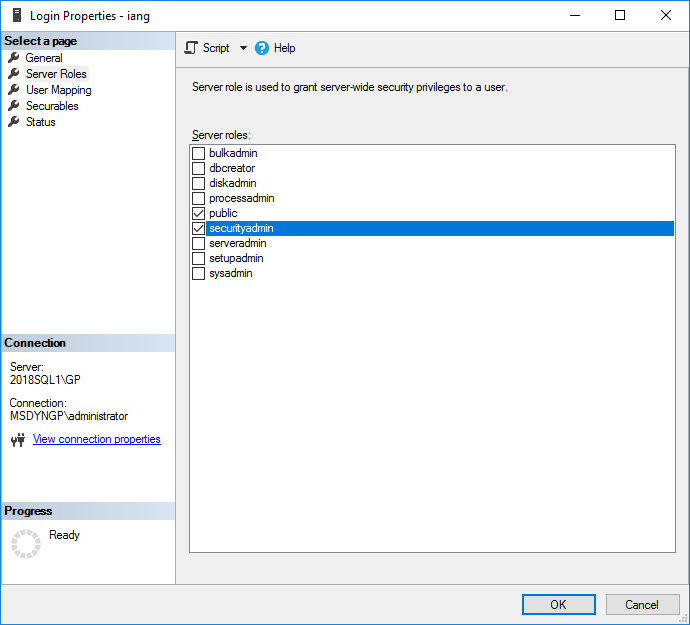
The next two steps are done through SQL Server Management Studio; Expand the Security and Logins nodes and double click the required user.
On the Server Roles tab, mark the securityadmin checkbox:
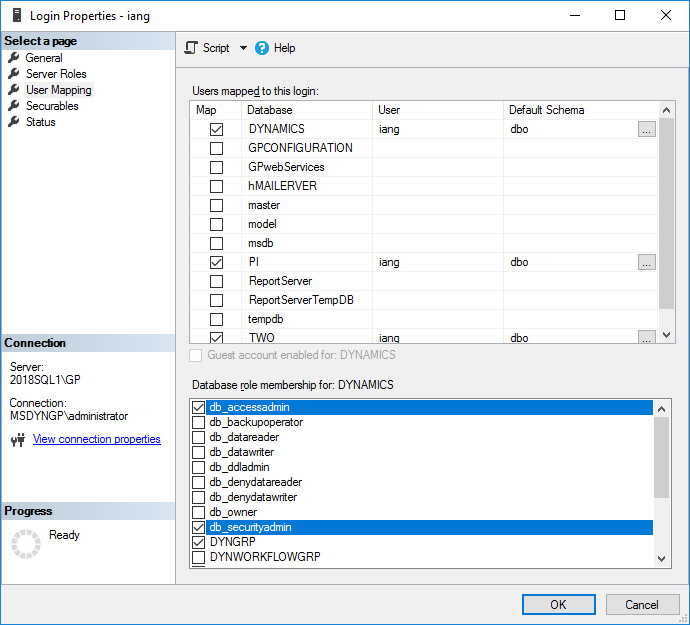
Move to the User Mapping tab and, for each of the GP databases, including the system database, mark the db_accessadmin and db_securityadmin checkboxes:
Click OK to save the changes and close the window. The user will now be able to create new users and assign access to companies.
What should we write about next?
If there is a topic which fits the typical ones of this site, which you would like to see me write about, please use the form, below, to submit your idea.





1 thought on “Create User or Assign Company Access Without Using sa”